Documentation Index
Fetch the complete documentation index at: https://docs.anyshift.io/llms.txt
Use this file to discover all available pages before exploring further.
Overview
Connect your AWS account to Annie to enable real-time infrastructure mapping, monitoring, and intelligent insights. Annie will ingest your AWS resources and relationships to build a comprehensive knowledge graph of your cloud environment.What Annie reads
The Terraform below creates an IAM policy that grants what Annie needs for the resource graph (bucket inventory and per-bucket metadata only — no object reads, no data-plane access):- S3: bucket inventory and per-bucket metadata (location, default encryption, event notifications, access points, multi-region access points). No object content is read for the resource graph.
- Compute, network, identity, monitoring, application, KMS, notifications, and other services:
Describe*/List*/Get*only. - No write actions. No
kms:Decrypt, nosecretsmanager:GetSecretValue(onlysecretsmanager:GetResourcePolicyfor resource policies, not secret material).
Setup Guide
- Go to the Anyshift integrations page
- Navigate to the AWS section
- Follow the setup instructions to connect your AWS account
Step 1: Create the IAM policy
Create a least-privilege managed policy that Annie will use. The same policy is reused by both Option 1 (Assume Role) and Option 2 (IAM User) below.Step 2: Grant Annie access
Option 1: IAM Assume Role (Recommended)
Option 1: IAM Assume Role (Recommended)
Create the IAM Role
- Using Terraform (Recommended)
- Using AWS Console
- Navigate to IAM Roles and select Create Role.
- Choose Another AWS account and enter the Account ID:
211125758836. - Add an External ID (Optional: Acts as a shared secret).
- Attach the
annie-readonlypolicy created in Step 1. - Complete the role creation process.
- Copy the Role ARN for the next step.
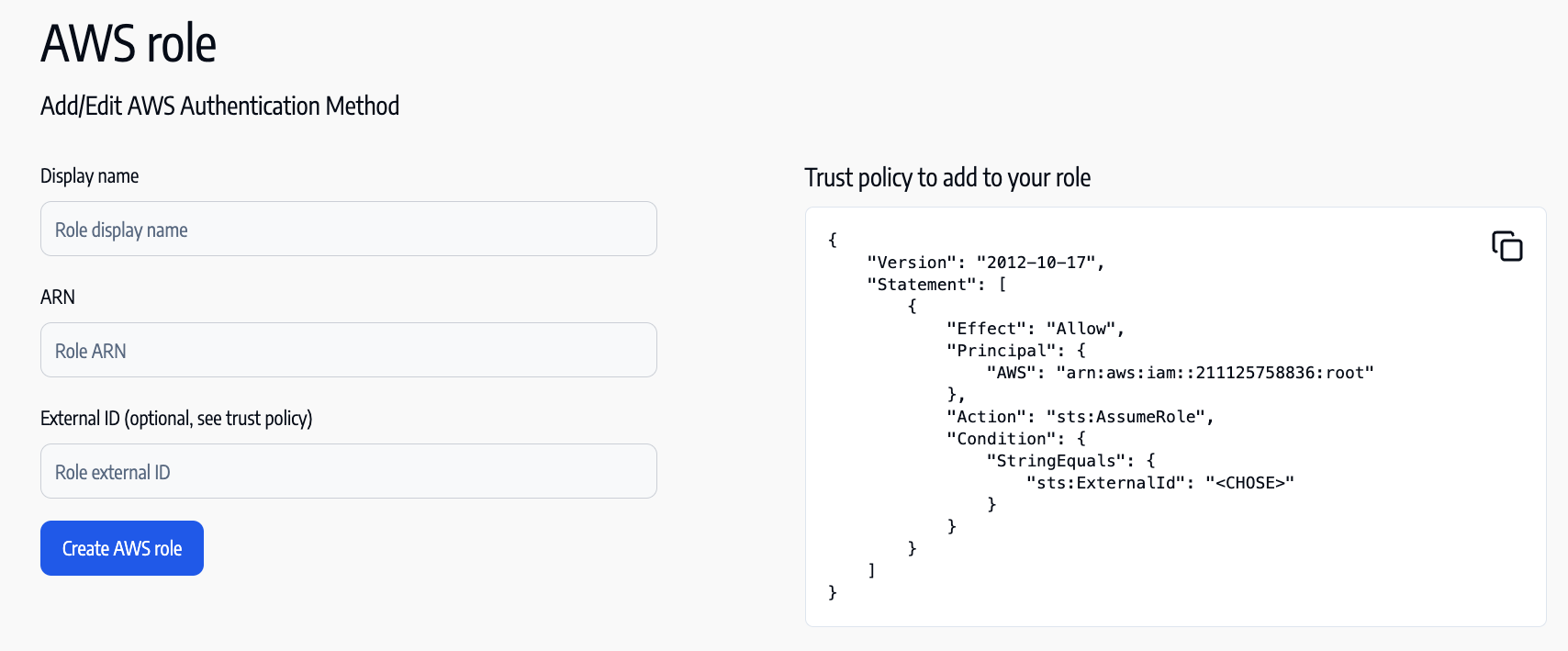
Add the IAM Role to Anyshift
- Navigate to Anyshift Configuration and select Add AWS Role.
- Enter a descriptive Display Name for the role (e.g.,
"read_only_role_for_anyshift"). - Paste the Role ARN from the previous step.
- Enter the External ID (Optional)
- Save the configuration.
Option 2: IAM User
Option 2: IAM User
Create the IAM User
- Using Terraform (Highly Recommended)
- Using AWS Console
- Go to IAM → Users → Add User
- Enable Programmatic Access
- Attach the
annie-readonlypolicy created in Step 1. - Save Access Key ID and Secret Access Key
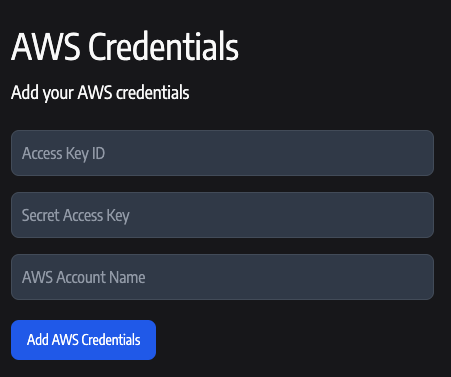
Configure in Anyshift
- Enter the Access Key ID and Secret Access Key you obtained from the IAM user creation step.
- Provide a descriptive AWS Account Name label (e.g.,
"read_only_user_for_anyshift").
Option 3: Restrict S3 to specific buckets (Optional)
Option 3: Restrict S3 to specific buckets (Optional)
Use this variant if you want Annie to introspect only certain S3 buckets. Bucket enumeration (The
s3:ListAllMyBuckets, s3:GetBucketLocation) cannot be resource-scoped at the IAM level — every bucket name and region will still be visible. Per-bucket metadata (encryption, notifications) will only be read for the buckets you list.Keep the data "aws_iam_policy_document" "annie_readonly" block from Step 1 unchanged. Add the blocks below in the same Terraform configuration, and change the policy argument on aws_iam_policy.annie_readonly from data.aws_iam_policy_document.annie_readonly.json to data.aws_iam_policy_document.annie_readonly_bucket_scoped.json.override_policy_documents argument replaces the original AllowS3Metadata statement (matched by sid) and appends the new AllowS3IntrospectionScoped statement.Tradeoff: buckets not listed in AllowS3IntrospectionScoped will appear in the Annie graph as bare entries (name + region) without encryption or notification attributes. S3 access points and multi-region access points are not bucket-scopable in IAM and are not introspected in this variant.Optional: Terraform state ingestion
If you store Terraform state in S3 and want Annie to ingest it (drift detection, IaC-to-live mapping), grant the same role/users3:GetObject and s3:ListBucket on your tfstate bucket(s) in addition to the policy above. Scope tightly to the buckets that hold state — Annie will only read keys you tell it to ingest, and only those grants are needed.
aws_iam_policy.annie_tfstate_read.arn to the same role (Option 1) or user (Option 2) using the same aws_iam_role_policy_attachment / aws_iam_user_policy_attachment pattern shown above. If your state is encrypted with a customer-managed KMS key, also grant kms:Decrypt on that key’s ARN.
Features Enabled
Resource Monitoring
Real-time visibility into your cloud infrastructure
Dependency Mapping
Understand your infrastructure dependencies
Try Annie Today
Start building your infrastructure knowledge graph and unlock intelligent infrastructure management.Create Account
Create your Anyshift account
Request Demo
See Annie’s knowledge graph in action